Localhost(127.0.0.1)
localhost
What is localhost?
The first point to make when explaining what a localhost is, is that it is always your own computer: when you call the localhost, your computer is talking to itself. However, this is a condensed approach. The localhost is not always directly identified with your computer. In most cases, it has a separate IP address like 192.168.0.1. within your personal network, which is different to the one you use on the internet, and is usually dynamically assigned by the internet service provider. When you are talking about a localhost, you are referring to when a server is used on your own computer.
Conversely, this means that the term is only used in the context of networks. “Localhost” is not just the name for the virtual server, but also its domain name. Just like .test, .example or .invalid,., .localhost is a top-level domain reserved for documentation and testing purposes. When you try to access the domain, a loopback is triggered. If you acces "http://localhost" in the browser, the request will not be forwarded to the internet through the router, but will instead remain in your own system. Localhost has the IP address 127.0.0.1, which refers back to your own server.
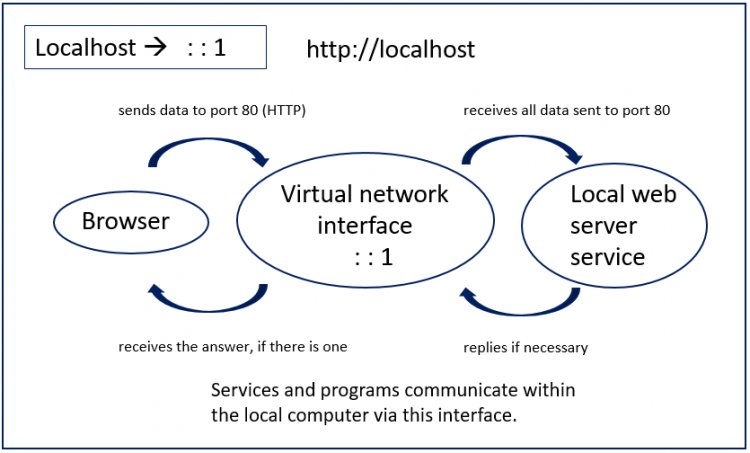
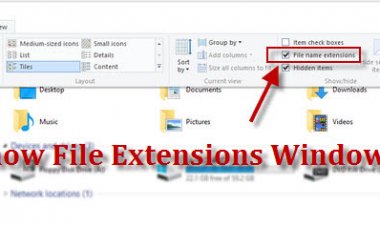
Exemplary representation of the communication between a web browser and web server within a local computer
127.0.0.1 – how does loopback work?
IP addresses are used within a network to communicate with each other. Each participant in the network has their own address. Data packets sent via TCP/IP are able to reach the correct destination when this system is used. The protocol pair Transmission Control Protocol (TCP) and Internet Protocol (IP) are some of the cornerstones of the internet. However, TCP/IP is also used outside the internet, in local networks. During transmission, the Internet Protocol is responsible for allowing the IP address and subnet mask to address subscribers in a network.
The allocation of public IP addresses (those that can be reached through the internet) is regulated by an international organization: the Internet Corporation for Assigned Names and Numbers (ICANN). ICANN is also responsible for the allocation of domain names, or the Domain Name System (DNS). However, certain address ranges are reserved for special purposes, like the range from 127.0.0.0 to 127.255.255.255. There is no reliable information on why that range was chosen, but you are free to speculate.
Until the 1990’s, IP addresses on the internet were divided into different classes. The first class (Class A) started with 0.0.0.0 (this address is also reserved) and ended with 127.255.255.255. 127 is the last block within the Class A network. This important position could have been the reason why it was chosen.
A Localnet can be set up within this address range. The special thing about this range is not only that it was reserved by ICANN, but is also that IP addresses are not uniquely assigned in it, as is usually the case. But how does it work?
With IPv6, the address ::1 is reserved for loopbacks.
For example, if you enter an IP address (or corresponding domain name) in your browser, the router will forward your request to the internet and to the correct server. This means that if you enter 172.217.0.0, you will reach the Google homepage. However, the situation is different with 127.0.0.1 because requests to this address will not be forwarded to the internet. TCP/IP recognizes from the first block (127) that you don’t want to access the internet, you are calling yourself instead. This then triggers the loopback.
Conversely, the protocol does not accept external requests addressed to 127.0.0.1, as it would mean that attackers could try to sneak into their system. Packets reportedly appearing on the internet from reserved IP addresses like 127.0.0.1 are known as Martian Packets.
A loopback device is created so that the back link to your own computer works. This is a virtual interface that is created through the operating system. With Unix systems, the interface is called lo or lo0 and can also be displayed using the ifconfig command. A similar command for Windows is ipconfig.
If you consider the technology independently of the local host, a loopback can be created in an analog way: circuits in communication technology can then be used to determine whether the paths taken by the signal and the reception are correct.
What is localhost used for?
Developers use the local host to test programs and web applications. Network administrators can also use the loopback to test network connections. Another practical use for the localhost is the hosts file, where you can use the loopback to block malicious websites.
For Testing Purposes
Localhost’s main use in web servers is for programming applications that need to communicate over the internet. During development, it is important to find out whether the application actually works as hoped once it has internet access. Localhosts’ other functions are only possible if the required files can be found on the internet - for example, there is a difference between opening a HTML document on your PC or loading it onto a server and accessing it. Releasing an unfinished product without testing it doesn’t make sense, so developers use a loopback to test them. They can stimulate a connection while also avoiding the network detour: the connection instead just stays completely inside their own system.
Another advantage of using localhost for testing purposes is its speed. When you send a request over the internet, it takes more than 100 milliseconds. If you send a ping to localhost, the maximum transmission time is just one millisecond. With this technology, you can also find out whether or not the Internet Protocol is correctly implemented. To test this yourself, just open the command prompt (Windows) or terminal (Unix/Mac) and use the ping command. You can either send it to the domain localhost or directly to the IP address.
ping localhost
ping 127.0.0.1
If you want to set up your own test server on your PC to address it through the localhost, you first need to install the right software. It is generally possible to run any standard web server on your own computer, but there is also special software specifically designed for use as a localhost – XAMPP for example. We provide a step by step guide for how to install and configure the test system in our Digital Guide.
To block websites
Localhost also plays a role in the hosts file. In principle, this file is a predecessor of the Domain Name System (DNS): in it IP addresses can be assigned to the corresponding domains. If you enter a website address in the browser, the domain name needs to be translated into an IP address. It used to be the host file, but today you would usually use the global DNS. However, the host file is still present in most operating systems. With Windows, you can find the file under \system32\drivers\etc\hosts; with macOS and other Unix systems, it is found under /etc/hosts.
If you yourself have not made any file changes, there are probably these two entries left:
127.0.0.1 localhost
::1 localhost
This ensures that name resolution for the localhost does not have to be done over the internet. You can also use the file to block certain websites. To do this, enter the website to be blocked into the list and assign the domain the IP address 127.0.0.1. If you – or perhaps a malicious script – try to call up the locked domain, the browser will check the hosts file first, and find your entry there. Another option is to use the domain name 0.0.0.0.
The browser will then try to access the corresponding website on the server with 127.0.0.1. However, it is unlikely that the browser will be able to locate it, because the requested file will not be there. However, if you have set up your own test server, then the browser may find home.html, but this is just your own file. If you have not set up your own test server, an error message will appear instead of the requested website. This technology can also be used to switch off ad inserts throughout the system. To not have to make every entry manually, you can find finished and regularly extended host files on the Internet.
The hosts file could have a major impact on your security when browsing the internet. Although the file is suitable for blocking malicious websites, criminals can still manipulate it too. You therefore need to make sure that you do not copy entries from other websites without checking them first, and also make sure that malware does not try to make entries without you realizing either.

 admin
admin